IT services designed for security, compliance, and continuity
Konverge Singapore delivers managed IT services, cybersecurity, and cloud solutions for organisations that depend on resilient and well-governed technology. Our services focus on reducing risk, improving visibility, and ensuring systems perform reliably across modern and hybrid environments.

PRIORITISING SECURITY, COMPLIANCE & SUSTAINABILITY
Why Konverge Singapore
Expanding from our established Australian operations, Konverge brings over two decades of enterprise IT experience into the Singapore market.
We combine regional expertise with local delivery capability to support:
Monetary Authority of Singapore (MAS) aligned solutions
PDPA-aware data governance
Secure cloud migration
Hybrid and modern workplace transformation
Enterprise procurement and lifecycle management
GLOBALLY TRUSTED COMPANY, LOCALISED SERVICING
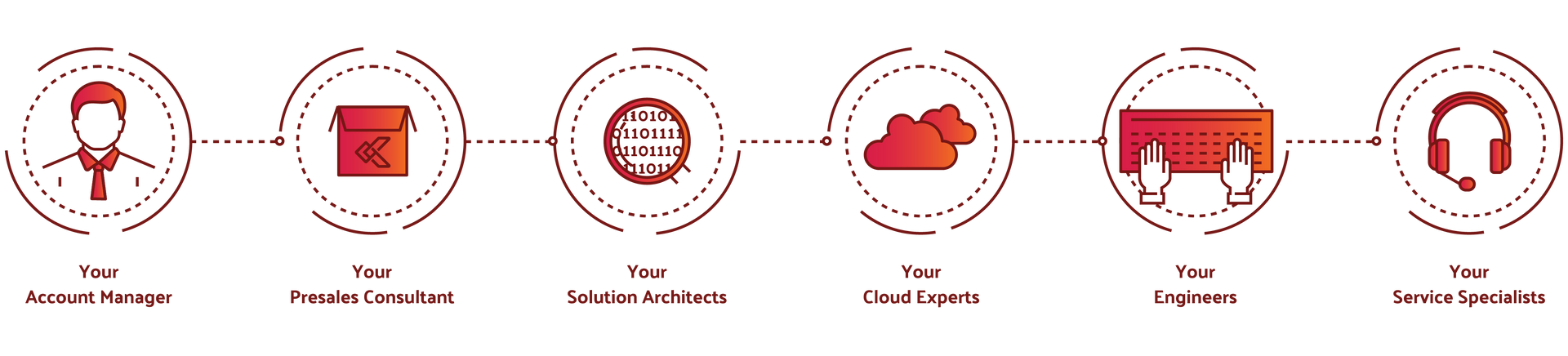
Our team is at your service
Our services are designed for organisations operating in regulated or risk-sensitive environments. We provide a single partner model that covers day-to-day IT operations, security oversight, and strategic guidance.
CONTINUOUS SECURITY & COMPLIANCE
Cybersecurity and risk management
We design and implement layered security architectures that protect identities, endpoints and infrastructure while aligning to regulatory expectations.
Services include:
- Endpoint and device security
- Conditional access and identity governance
- Data loss prevention and encryption
- Compliance monitoring and reporting
- Security policy design and enforcement
Outcome: Reduced risk exposure and improved audit readiness.

SECURE & SCALABLE DESIGN FOR PERFORMANCE & COST CONTROL
Hybrid IT & Cloud Infrastructure
We help organisations strengthen their security posture through practical controls, monitoring, and response capabilities. Our approach prioritises risk reduction, visibility, and alignment with regulatory and business requirements.

SIMPLIFIED DEVICE FLEET PROCUREMENT & MANAGEMENT
Procurement, Licensing & Device Lifecycle
Simplify sourcing, rollout and refresh programs with rapid quoting and transparent pricing. We can also manage device onboarding, configuration baseline, patch orchestration, compliance reporting (Intune/endpoint management aligned to BYOD/device management patterns described in MAS guidance).

ALWAYS ON-SUPPORT, PROACTIVE MONITORING & SECURITY
Managed IT & Professional Services
Operate and secure your Microsoft estate with a managed services partner built for uptime, governance and continuous improvement. We manage day‑to‑day operations across endpoints, Microsoft 365 and Azure—so your team can focus on transformation.

SERVICES MADE SIMPLE
Flexible As-A-Service Models
At Konverge, we help our customers maximise the return on IT investments by supporting the full lifecycle of your key IT initiatives, from assessment then design to deployment and on-going management.
Software as a Service
We have the marketplace to assist with your software subscriptions, providing single billing, dedicated software experts
Infrastructure as a Service
We can provide customise infrastructure resources to specify levels of CPU, RAM, storage, internet data, storage speed. Get your application up an running in minutes with a Konverge virtual server
Device as a Service
We deliver cloud-based virtual desktops enable our customers to rapidly provision a desktop to any user on any device, anywhere, all with centralised security and management.
Network as a Service
We deliver network connectivity enabling our customers to build out their own private network or help provision network connectivity. Services include VPN, MPLS, SD WAN or dedicated dark fibre connectivity
EXPERT MICROSOFT SUPPORT ACROSS MOBILE DEVICES TO CLOUD INFRASTRUCTURE
Microsoft Support & Services
Whether you require ongoing managed services, project implementation or optimisation support, our team provides practical, compliance-aware expertise across the Microsoft ecosystem.

Mobile Device Management
Secure and manage devices across your workforce with confidence.
Our services include:
- Device enrolment and configuration
- Policy design and compliance enforcement
- Application deployment and management
- Conditional access configuration
- BYOD governance frameworks
- Security hardening and monitoring
We help organisations simplify multi-device management while protecting sensitive data and ensuring regulatory alignment.

Microsoft SharePoint
Empower collaboration while maintaining structured governance.
Our SharePoint services include:
- SharePoint Online deployment and migration
- Information architecture design
- Governance and permissions management
- Workflow and automation configuration
- Document lifecycle and retention policies
- Integration with Microsoft 365 ecosystem
We ensure SharePoint environments are structured, secure and scalable to support long-term growth.

Microsoft Intune
Modern endpoint management with enterprise-grade security.
Our Intune expertise includes:
- Zero Touch deployment configuration
- Endpoint compliance policies
- Application protection policies
- Conditional access integration
- BitLocker and encryption configuration
- Reporting and compliance monitoring
By aligning Intune with your broader cloud strategy, we help reduce reliance on on-premise infrastructure while improving visibility and control.

Microsoft Azure
Secure, scalable cloud infrastructure designed for performance and resilience.
Our Azure services include:
- Cloud readiness assessments
- Azure migration planning and execution
- Identity and access management
- Network security architecture
- Cost optimisation and governance
- Backup, disaster recovery and business continuity planning
We support hybrid and cloud-first strategies that balance performance, compliance and cost efficiency.
CASE STUDY
Microsoft Intune for Education
Enhancing security and improving productivity at the Maitland Christian School with Microsoft Intune.

KONVERGE PROCESS TO SUCCESS
Let your business flow
We’re already helping many businesses just like yours simplify their security, reduce risk, and feel more in control, and we’d love to help you too.

Analysis
STEP 1
Evaluate business objectives, technology environments and processes. Identify opportunities for performance improvements and cost savings.
STEP 2
Design
Recommend relevant technologies and services, document technical architecture, deployment plans, measure of success, budgets and timelines.
STEP 3
Procure
We work with multi-vendors to get support with demos, proof of concepts. We engage the key account managers for best pricing structures.
Deploy
STEP 4
Assist with product fulfilment, configuration, implementation, integration and training. Our project managers will ensure each solution are delivered properly and promptly.
STEP 5
Manage
Proactively monitor systems to ensure technology is running as intended and provide support when and how you need it.
STEP 6
Scale
We regularly touch base to need understand the organisation long term goals. We help scale out projects to the customer's desires.
FEQUENTLY ASKED QUESTIONS
FAQs
What types of organisations does Konverge Singapore work with?
We work with growing and regulated organisations that require reliable, secure, and well-governed technology. Our clients include professional services firms, healthcare providers, financial services organisations, logistics companies, and regional headquarters.
Do you provide local support in Singapore?
Yes. Konverge Singapore provides local support and account management, backed by global standards and shared operating frameworks across the Konverge group.
How do you approach cybersecurity?
We take a security-first approach that focuses on prevention, visibility, and response. Our services are designed to reduce risk, support governance requirements, and integrate with existing IT environments rather than replace them unnecessarily.
Do you replace internal IT teams?
No. We work alongside internal IT teams where they exist, providing additional capacity, specialist expertise, and operational support. Our role is to strengthen capability, not remove control.
How do you support remote and distributed teams?
We design and manage modern workplace environments that secure identities, devices, and access to systems. This enables staff to work remotely or across regions without increasing operational or security risk.
Can you support organisations operating across multiple regions?
Yes. We support organisations with operations across Australia, Singapore, and the United States. Our services are designed to provide consistency while accommodating regional requirements.
How do you handle compliance and regulatory requirements?
We align technology decisions with regulatory and governance expectations by applying appropriate security controls, documentation, and oversight. We work with clients to support audits and compliance reviews where required.
Do you work with specific technology vendors?
We work with a range of established technology partners, including Microsoft and leading cybersecurity vendors. Our recommendations are based on suitability and risk requirements rather than vendor preference.
What is your engagement model?
We operate on a long-term partnership model with clear ownership, defined responsibilities, and regular reviews. This ensures accountability and consistent outcomes over time.
How do we get started?
The first step is an initial discussion to understand your environment, risks, and objectives. From there, we recommend a practical next step aligned to your priorities.



